 By choosing Northwest Data Restoration, you get the assurance that we cannot take pointless dangers along with your necessary information. This can be a software created by Entry Knowledge. It helps in viewing and imaging storage devices. Its effectiveness at information recovery is pegged on the time when the file was deleted. It might probably generate MD5 hash values of seen and accessible data. The MD5 hash worth is created and given to the investigator as a chunk of the finished operation; this warrants the authenticity of the original knowledge.
By choosing Northwest Data Restoration, you get the assurance that we cannot take pointless dangers along with your necessary information. This can be a software created by Entry Knowledge. It helps in viewing and imaging storage devices. Its effectiveness at information recovery is pegged on the time when the file was deleted. It might probably generate MD5 hash values of seen and accessible data. The MD5 hash worth is created and given to the investigator as a chunk of the finished operation; this warrants the authenticity of the original knowledge.
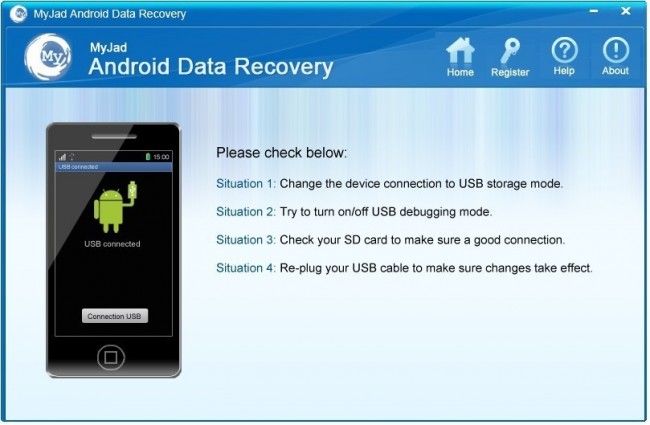
Generally, data present in the physical drives (Internal/External Arduous disk, Pen Drive, etc) gets lost, deleted and formatted due to circumstances like virus attack, accidental deletion or unintentional use of SHIFT+DELETE. In these cases, data restoration software are used to get better/restore the info recordsdata.
Given that Samsung is making such a big deal about how Bixby might be contextual and understand what you need, if you need, it appears odd that it is being launched now at all. Google Assistant remains to be out there on the Galaxy S8, and is arguably far more useful. As an illustration, you may nonetheless say ‘Okay Google’ and do all of the things Bixby can and extra… while not having to press a dedicated button.
Criminals perpetrate these crimes by discovering vulnerabilities in software and operating methods of computers linked to the web. Once a loophole is found, the criminal can entry or store delicate information on some form of storage media. This may be local i.e. on removable drives comparable to zip drives, compact disks or reminiscence sticks. It could possibly also contain exhausting drives. When such crimes are dedicated, a prosecution is generally an uphill process as a result of the crime scene may involve totally different cities and unsuspecting third parties (Boyd and Forster: 2004). It’s at this level that a forensic specialist is tasked with combing by way of the digital crime scene by neutrally scrutinizing a variety of digital material concerned or presumed to be involved within the crime and at last produce a report summarizing the contents of the fabric under investigation.
Step 2: Open the restoration software you’ve got just installed. Click ‘Start’ to initialize a scanning process. Lastly, you need an internet service provider to supply an web connection like Cable, DSL, Wi-fi Web to your own home or office. This is just like Siri that I exploit on my iPad. It really works, and it even underlines words that it isn’t positive it understood. However you do have to be cautious as it sometimes types something completely different than what you meant, simply because it sounds the same.




More Stories
What are the roles of civil engineers in construction projects?
A Developer’s Dream: Achieving Full Stack Mastery with Logicmojo
Top 5 Benefits of Working with a Professional Locksmith